CISCO Stealthwatch Free Training - Lesson 1
Cisco Stealthwatch is a complete network visibility and security analytics.
With stealthwatch solution, you can gain visibility across the entire network. You can also improve segmentation efficiency across the network.
If I want to explain stealthwatch in another way, I can say Cisco Stealthwatch: Is a collector and aggregator of network telemetry to have security analysis, and to monitor.
This visibility is coming from Netflow. If we activate NetFlow on all of our network devices, we will have a trace of every moving packet in our network, north-south or east-west.
Solution Components
In the Cisco stealthwatch solution, we have core components and optional components.
Core Components:
1. SMC
2. Flow Collector
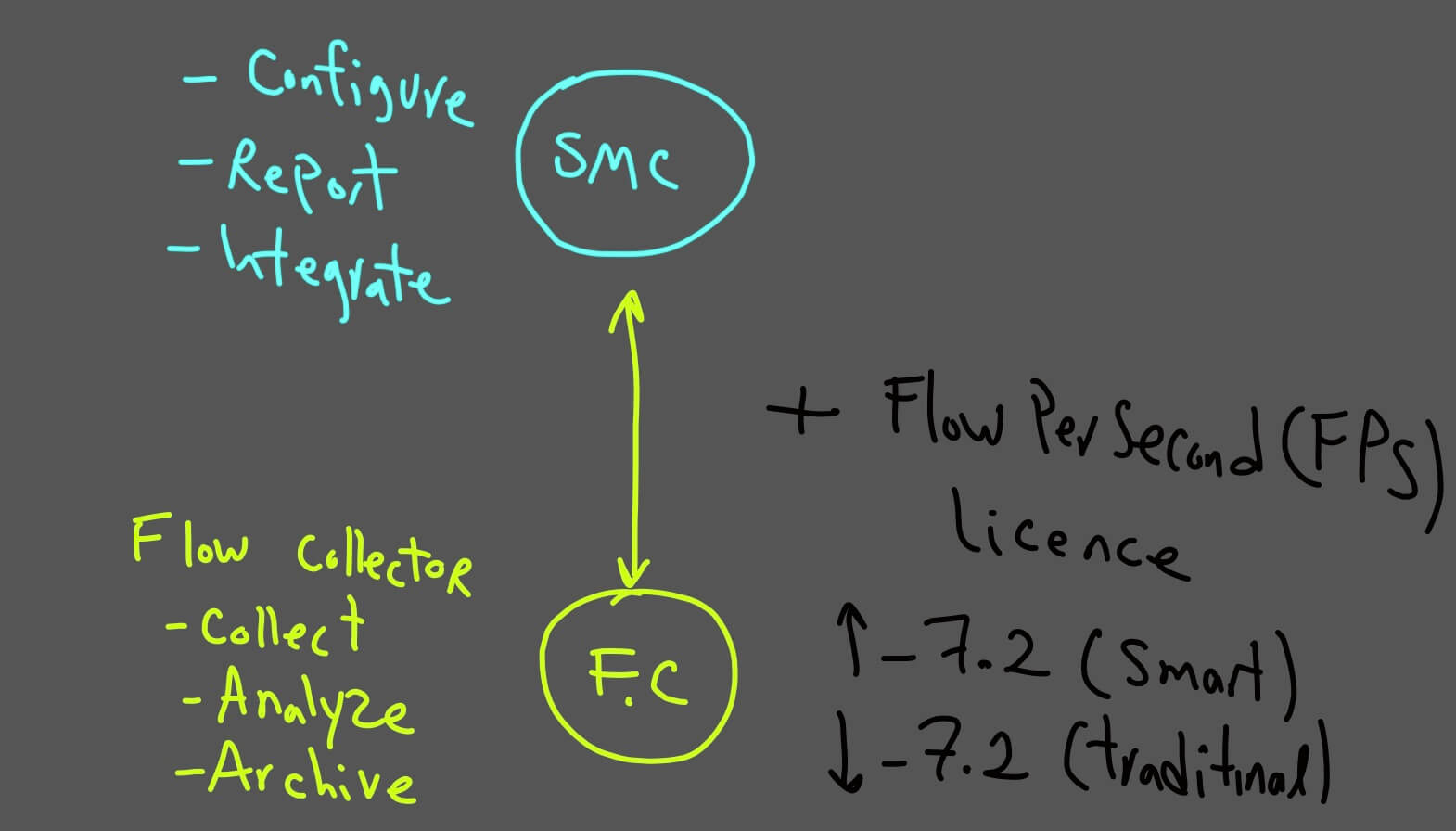
SMC
We do all Configuration, Monitoring & Integrations, and it will do reporting for the solution. We can have a maximum of 2 SMC in our deployment ( HA), it can be virtual or physical.
SMC provides a graphical interface, so it's straightforward to understand and user friendly. In the recent version, instead of java interface, we can download the app and configure the SMC through its app.
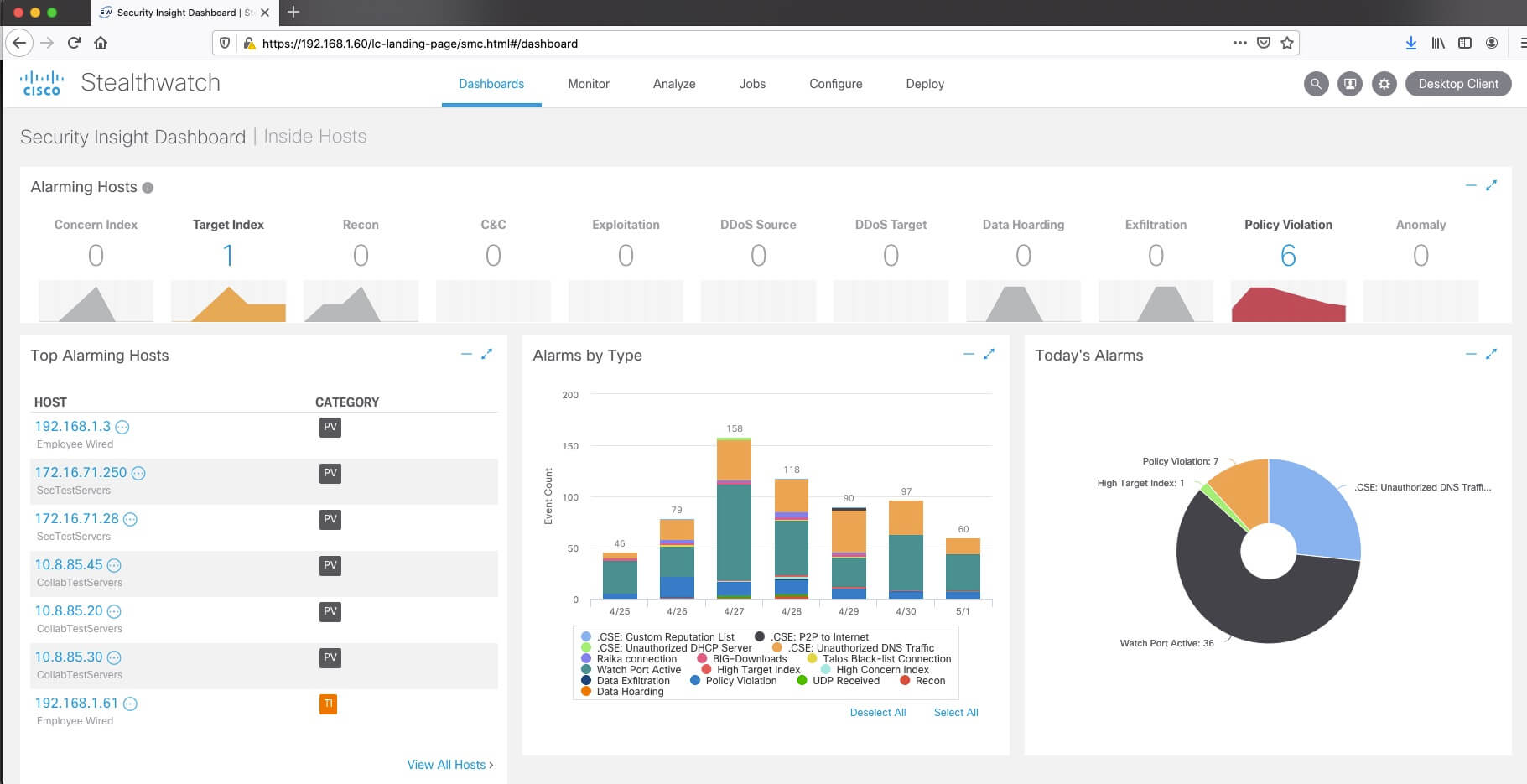
As you can see in the screenshot, SMC displays multiple alarm categories on its dashboard. This easiness is very important for a soc administrator or team to act fast.
Flow Collector
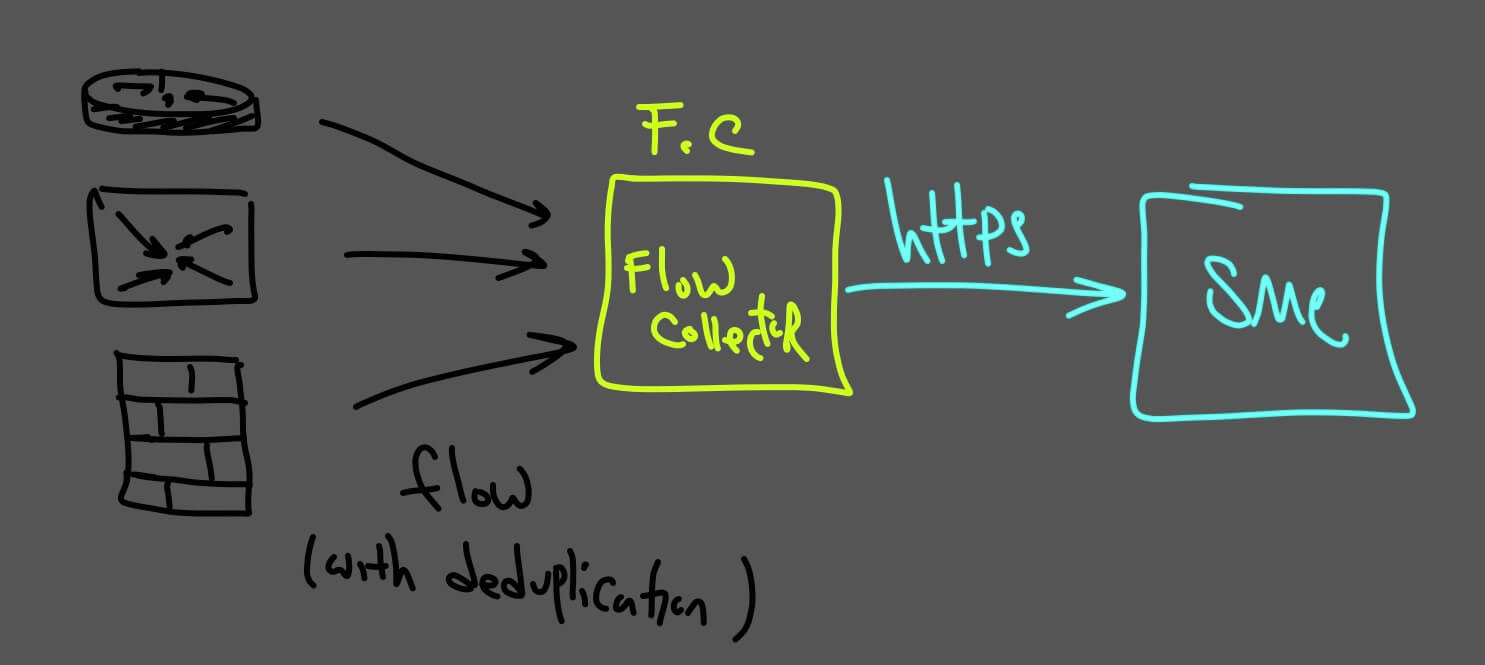
It will collect all the Netflow traffic from devices like firewalls, router, or switches, and the flow database is in this component.
We have different collectors for NetFlow/IPFIX and sflow
this also can be virtual or physical, and the maximum number of FC per deployment is 25.
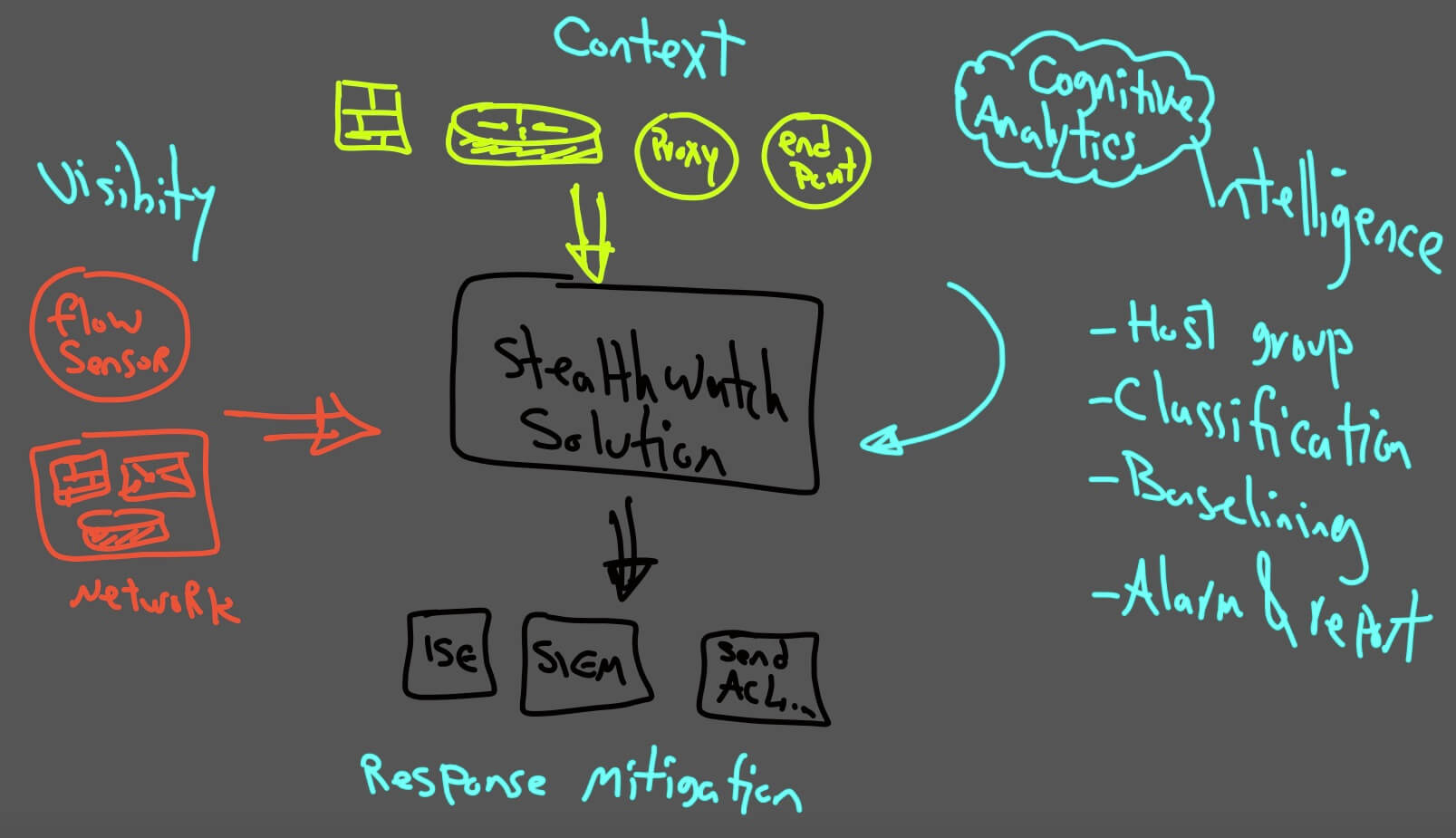
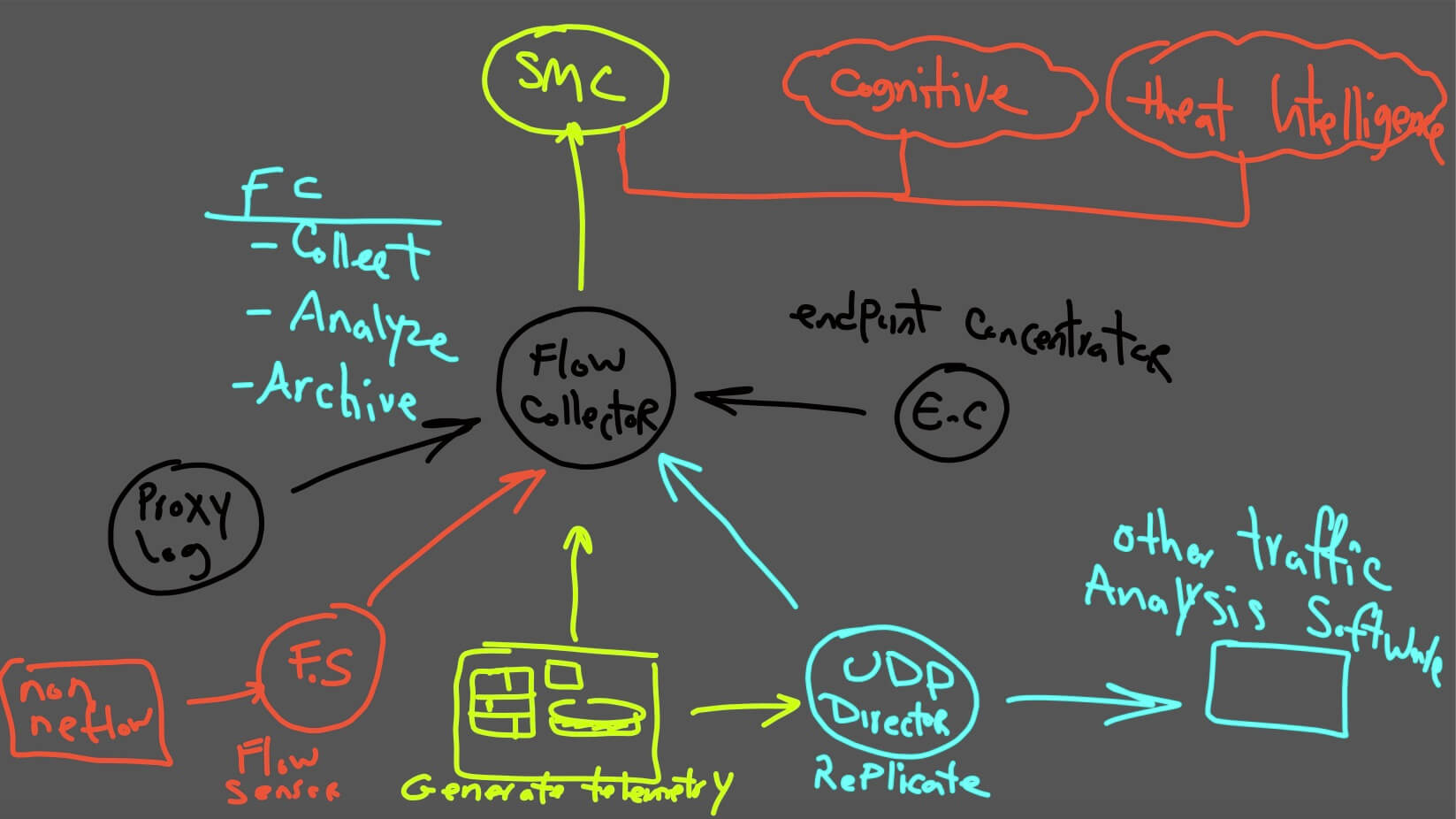
Solution Intro
As you can see in the graph that Cisco stealthwatch will collect context information and flow from all types of network devices, it will then classify, and it will create a baseline for almost everything, even your printer! And then, based on the machine learning algorithm and all the intelligence from cognitive, it will alarm you and report you about network security or even performance issues.
You can also integrate it with other mitigation solutions like Cisco ISE, or even you can push a null0 route to your end device for bad traffic.
In my opinion, it's a very robust solution for before and after an attack.
Optional Components:
-
Flow Sensor
-
UDP Director
-
Endpoint Concentrator
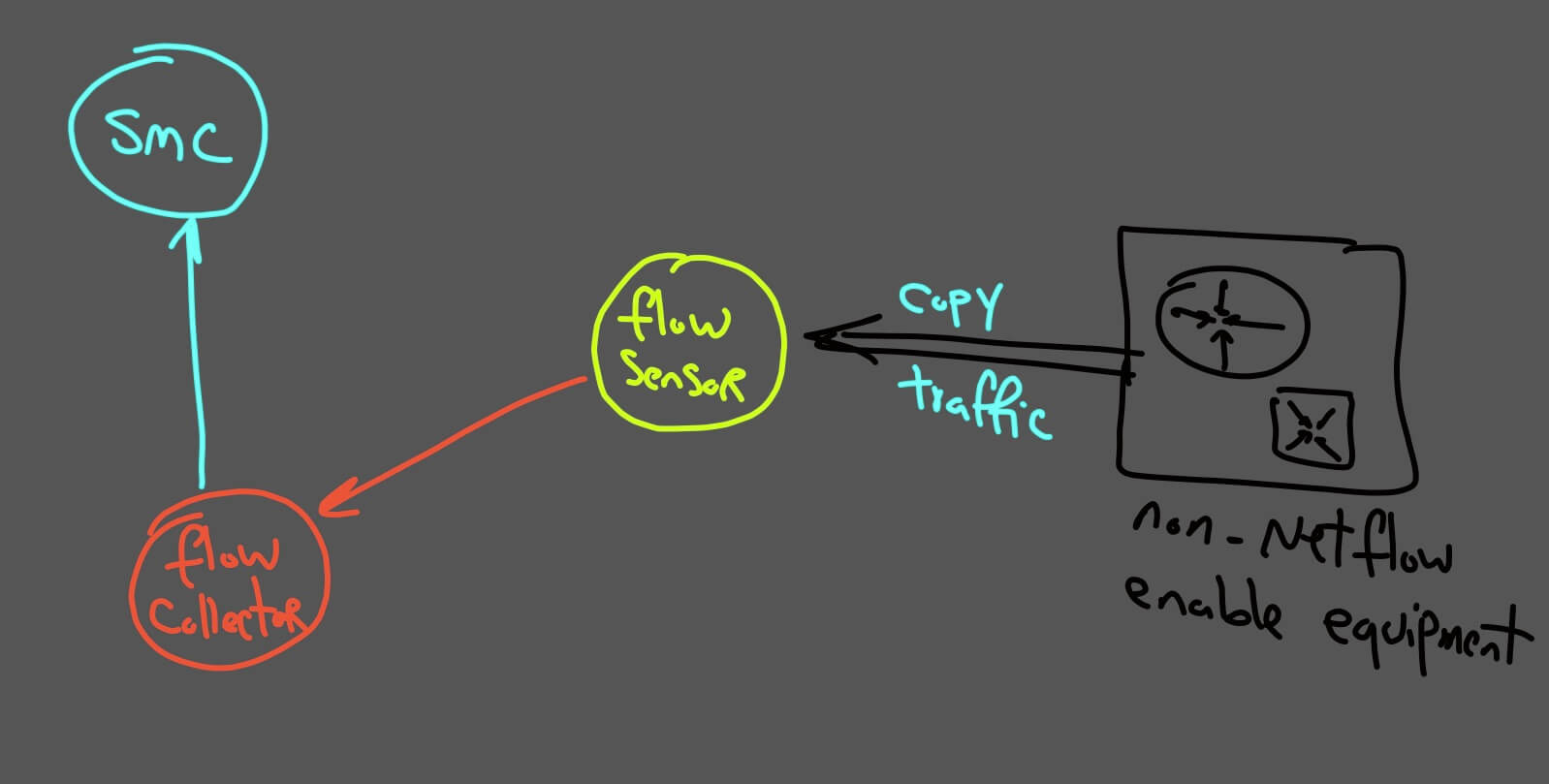
Flow Sensor
What if our devices in the network don't support NetFlow at all?
Like Cisco Catalyst 2960?
In this case, we can copy our traffic with span or RSPAN.
Flowsensor can be the destination of this copies traffic,then flow sensor will produce Netflow and will send to flow collector.
Flowsensor can be a physical or virtual appliance.
UDP Director:
Allows Netflow, Syslog and SNMP data to be sent transparently to multiple collection points. It can repeat traffic to numerous Flow Collectors.
UDP Director can also be a physical or virtual appliance./p>
Endpoint Concentrator:
By installing Cisco anyconnect visibility module, we can send flow directly from our endpoints to the flow collector via the "endpoint concentrator" appliance.
The total solution is very similar to this diagram:
In our next lesson (video lesson) I will show you how easily we can install and integrate them, and then will together go deep.
Thank you, and I hope you enjoy it.
